WordPress.org began testing two-factor authentication (2FA) as an opt-in feature in May 2023. The interface and functionality are still in beta but it’s operational. This week contributors have expanded support for 2FA with a new interface for adding security keys, which are more secure than the one-time passwords.
A logged in user can set up the keys by visiting their WordPress.org profile, scrolling down to the “Security” section, and clicking on the support forum profile link.
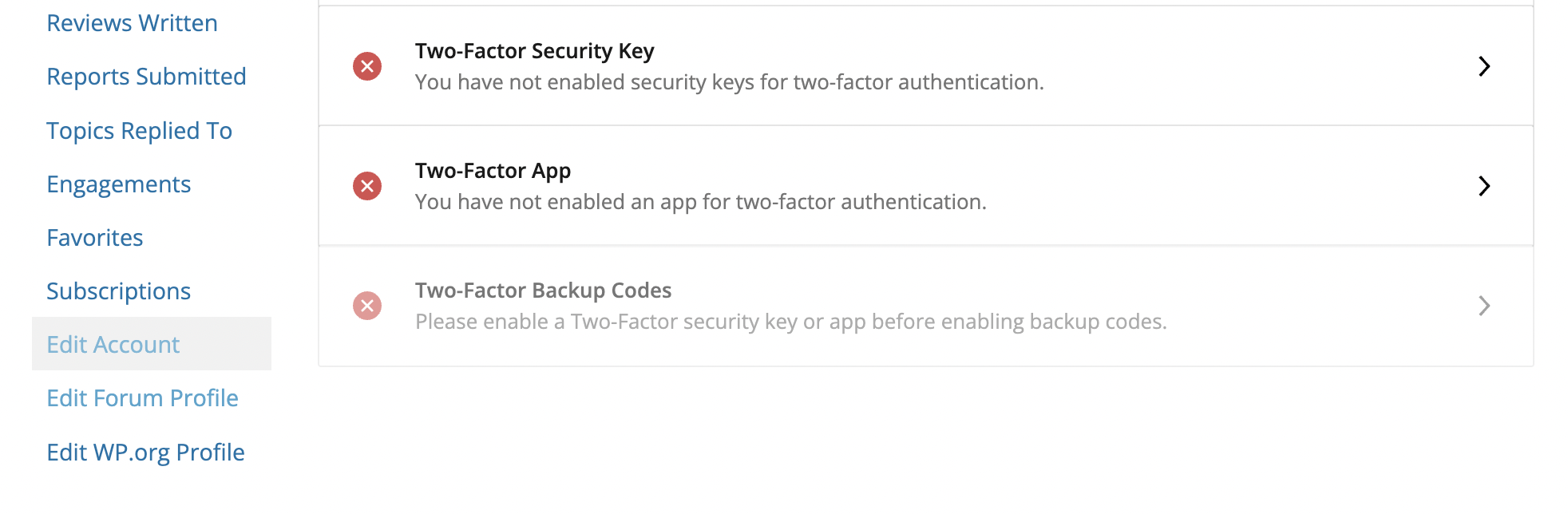
Users who have two-factor authentication set up can click on “Two-Factor Security Key” and follow the instructions to set them up.
This update to the interface also adds Time-Based One-Time Passwords (TOTP), which are generated from the user’s chosen authentication app on their device and changed every 30 seconds. WordPress.org currently defaults to using security keys over the time-based on-time passwords, but contributors are working on making that configurable in the future.
Additions to the interface also include the ability to generate backup codes, which enable access when users don’t have their 2FA security key or app configured. The backup codes come with a note of caution from Automattic- sponsored Meta contributor Steve Dufresne, who has been working on the 2FA project:
Regardless of whether you are using security keys or a Time-Based One-Time password, make sure you generate and print backup codes. If you lose your primary key/device and don’t have a backup code, you will lose access to your account forever.
Dufresne encouraged WordPress.org users who haven’t set up 2FA to go ahead and do so. Any bugs can be reported to the project’s GitHub repository.

